You Are the Target: What Law Enforcement Officers Need to Understand About Doxxing
Most officer safety training is built around the physical. Defensive tactics, firearms, vehicle dynamics, de-escalation under pressure. The threats that get the most curriculum time are the ones that manifest in the physical world — at the traffic stop, in the domestic call, in the foot pursuit.
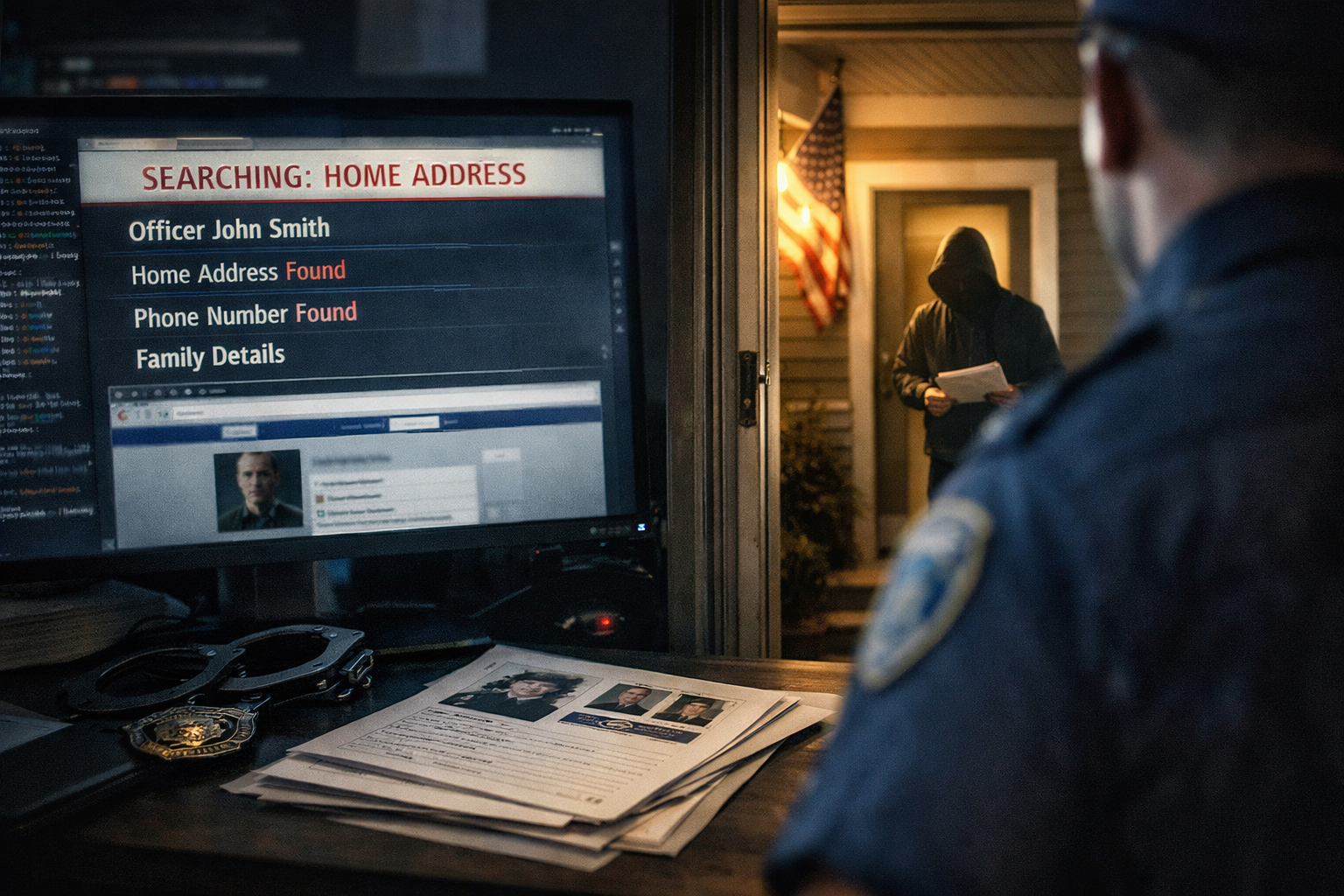
Doxxing doesn't fit that framework. It begins in a browser window, moves through a data broker website or a compromised account, and culminates in a spreadsheet of personal information posted to a forum or a social media thread with a call to action attached. Nothing physical happens — until it does.
That gap between the digital origin and the real-world consequences is exactly what makes doxxing difficult to take seriously as a threat until it's too late. By the time an officer's home address, spouse's name, children's school, and vehicle description have been circulating for 48 hours, the threat surface has already expanded far beyond what most incident response protocols are designed to address.
This piece is about understanding doxxing as the threat it actually is — not just as a privacy inconvenience, but as a tactic with documented connections to physical harm, a specific psychology of targeting that law enforcement officers should recognize, and a defense that requires sustained proactive effort rather than reactive response.
What Doxxing Actually Is and How It Works
The term has become common enough that it gets used loosely, which creates confusion about what the threat actually involves. Doxxing — derived from "document drop" — is the deliberate public release of private identifying information about a specific individual, usually accompanied by a social call to action designed to mobilize harassment, threats, or physical action against that person.
The information itself is rarely obtained through sophisticated hacking. Most successful doxxing operations are built almost entirely from publicly available data, aggregated across sources that individually seem innocuous. A name plus an employer plus a city of residence is usually enough to initiate a search on data broker sites that will return a home address, phone number, family members' names, associated vehicles, and historical addresses. That process takes minutes and requires no technical expertise.
What makes law enforcement officers particularly vulnerable is the asymmetry between their public-facing role and their desire for private lives. Officers are public officials whose names appear in police reports, court documents, local news coverage, use-of-force disclosures, and departmental press releases. Their professional identity is a matter of public record in ways that create a starting point for searches that most private citizens don't have. Once someone has a name and a badge number, the aggregation work is largely done for them.
The social layer is what transforms a privacy breach into a threat. Doxxing in isolation — private information released to no audience — accomplishes nothing. The harm comes from distribution to a motivated audience: a forum, a social media platform, an activist network, a group with specific grievances against law enforcement or against a specific officer. The doxxer is typically less interested in personally confronting the target than in mobilizing others who might. This crowd-sourcing of harassment is what makes doxxing scalable in a way that individual threats are not, and it's what makes the threat surface so difficult to bound once the information is out.
The Psychological Architecture of Being Doxxed
The physical security conversation around doxxing is important and gets covered reasonably well. The psychological conversation is largely absent, and it deserves more attention.
Being doxxed is a specific kind of violation that doesn't map cleanly onto other threat categories in law enforcement. It's not a physical confrontation. It's not an administrative action. It's the experience of having the boundary between your professional identity and your private life — between who you are at work and where your children sleep at night — deliberately and publicly collapsed.
For officers who have spent careers carefully maintaining that separation, the psychological impact of doxxing can be significant and specific. There's the hypervigilance that activates when you know your address is circulating online — the altered relationship with your own neighborhood, with your children's school drop-off, with the vehicle parked in front of your house. There's the loss of what threat researchers call environmental security: the baseline sense that your home and family are protected from the professional risks of the job. When that separation is violated, the stress load doesn't stay at work anymore. It follows you home, literally.
There's also a particular kind of anticipatory anxiety that doxxing generates — the experience of a threat that is real and documented but without a clear actor, a clear timeline, or a clear endpoint. The officer knows the information is out there. They don't know who has seen it, who might act on it, or when. That uncertainty is not a minor psychological inconvenience. It is a chronic stressor that, over time, produces the same physiological and psychological effects as other forms of prolonged threat exposure: disrupted sleep, hypervigilance, impaired concentration, relationship strain, and compounding occupational stress on top of an already demanding baseline.
Law enforcement has gotten better at recognizing and addressing the psychological toll of critical incidents — shootings, line-of-duty deaths, traumatic calls. It has barely begun to grapple with the psychological toll of persistent digital threat exposure, which is a different kind of injury with a different timeline and a different symptom profile. Officers who are managing the aftermath of being doxxed need support that recognizes the specific nature of what they're dealing with, not a framework designed for post-critical-incident response that doesn't fit.
Who Gets Doxxed and Why: The Targeting Logic
Understanding why specific officers get targeted is useful for both risk assessment and for making the threat feel less random and therefore more manageable.
The most common targeting triggers in law enforcement doxxing fall into a few categories.
Critical incident involvement is the highest-risk category. Officers involved in use-of-force incidents, particularly those that receive significant media coverage or generate public controversy, are primary targets. The targeting is often organized, beginning within hours of the incident becoming public, and can involve coordinated campaigns across multiple platforms to aggregate and distribute personal information. The speed of this response — accelerated significantly by social media — means that the protective window between an incident becoming public and an officer's personal information beginning to circulate is often measured in hours rather than days.
Participation in specific enforcement actions is an increasingly common trigger. Officers involved in politically charged enforcement operations — immigration enforcement, protest policing, enforcement actions in communities with significant local opposition to police — are targeted with increasing frequency. This category has grown substantially as activist networks have become more sophisticated in surveillance documentation and personal information aggregation.
Individual grievances from people who feel they were wrongly treated in an encounter with a specific officer represent a persistent lower-level risk. A person who received a citation they consider unjust, or who felt disrespected in an encounter, or who has an existing grievance against law enforcement, may initiate a targeted doxxing campaign against a specific officer using nothing more than a name from a police report and a search engine.
Incidental targeting — being identified as law enforcement through a social media post, a photograph, or a public appearance and targeted based on the profession rather than any specific incident — is the most diffuse category and the hardest to defend against proactively.
The common thread across these categories is that the targeting logic is mostly external to the officer's control. The incident happens, the enforcement action happens, the citation gets written — and someone on the other side decides to retaliate digitally. What officers can control is how much usable information is available when that search begins.
The Data Ecosystem That Makes Doxxing Possible
Most officers underestimate how much personal information is already publicly accessible about them before any hostile search begins. Understanding the ecosystem is a prerequisite for reducing the target profile.
Data broker sites — the commercial background check services that aggregate property records, voter registration data, court records, and other public databases — are the primary infrastructure of the doxxing economy. There are dozens of them, they update continuously as public records become available, and they collectively hold a detailed picture of nearly every American adult: current and historical addresses, associated family members, vehicle registrations, phone numbers, and email addresses.
Most of these sites have opt-out processes, but the process is fragmented — each site has its own removal mechanism, most require ongoing attention rather than a single permanent removal, and the data they hold is refreshed from public sources regularly, meaning an opt-out achieved today may need to be repeated in six months. This is tedious work, and there are commercial services that will manage it continuously for a fee. For officers with meaningful threat exposure, the investment is worth serious consideration.
Social media is the second major data source, and here officers have considerably more direct control. Personal accounts that include location tagging, family photographs with identifiable background details, check-ins at regular locations, or information about children's schools and activities are providing a running intelligence feed to anyone monitoring them. The privacy settings on most platforms default to more openness than most users realize, and the settings change frequently enough that what was configured correctly six months ago may not still be. This requires active rather than one-time management.
Professional information — LinkedIn profiles, departmental websites, court appearances, news coverage — is largely unavoidable but worth auditing for what it reveals. A LinkedIn profile that lists an employer, years of service, and unit assignment provides a meaningful starting point for more specific searches. A departmental website that includes photographs of named officers provides both identity confirmation and potentially usable imagery. Neither of these is controllable by the individual officer, but awareness of what's out there matters for risk assessment.
The metadata attached to photographs is a frequently overlooked vulnerability. Photos taken on smartphones embed GPS coordinates, device information, and timestamps in the image file by default. A photograph posted to any platform may contain precise location data even after the platform strips visible location information from the post. Officers who share photographs — particularly photographs taken at or near their residence — should understand this and configure their devices accordingly.
The Family Dimension
The aspect of doxxing that officers find most psychologically destabilizing, consistently, is not the threat to themselves. It's the threat to their families.
Doxxing campaigns targeting law enforcement officers routinely include family members in the released information — spouses' names and workplaces, children's names, schools, and activities, extended family members' addresses. This isn't incidental. It's deliberate. The tactical logic is that an officer who doesn't respond to threats against themselves may respond to threats against people they feel responsible for protecting. The family becomes both a pressure point and a softer target.
This requires that the protective conversation extend beyond the officer. Spouses and adult family members who maintain active social media presence, who are listed on data broker sites under a shared address, or who haven't been briefed on what information to avoid posting are extending the attack surface regardless of what the officer has done to harden their own profile.
Children present a specific and sensitive dimension. The information that gets routinely posted about children on social media — school photos with identifying captions, sports team photographs that tag a school or league, birthday posts that disclose full names and ages — can be aggregated into a detailed profile of a child's routine and location that most parents would find alarming if they saw it assembled in one place. For officers with elevated threat profiles, this is not a hypothetical risk. It has materialized in documented cases.
Having a clear, age-appropriate family conversation about digital hygiene — what gets posted, what privacy settings are set, what information family members share with others about the officer's identity and location — is uncomfortable and often gets deferred. It is also genuinely important.
The Threat-to-Action Pathway: When Doxxing Becomes Physical
Most doxxing campaigns against law enforcement officers do not result in physical violence. This is true and worth stating clearly, because allowing the threat to feel maximally catastrophic at all times is its own form of harm.
But the pathway from doxxing to physical threat is documented well enough that it cannot be dismissed, and understanding it is useful for both risk assessment and response prioritization.
The pattern that threat assessment research identifies most consistently is the role of doxxing in lowering the barrier to action for individuals who were already in a state of grievance and escalating ideation. Most people who see doxxed information about an officer will do nothing with it. A small number will send harassing messages or make calls. A very small number — the ones who were already moving along a threat trajectory before the doxxing occurred — may use the information to locate a target they had already decided to confront.
In this model, doxxing functions less as the proximate cause of physical threats and more as a force multiplier for individuals who were already dangerous. The information doesn't create the threat — it removes a barrier. The officer who was already in the crosshairs of a behaviorally concerning individual becomes a located target instead of a professional identity without an address.
This is why doxxing incidents warrant genuine threat assessment rather than either dismissal or maximum alarm. The question to answer is not "will someone act on this information" in the abstract, but "is there any individual in the population of people who have been exposed to this information who shows behavioral indicators of pre-attack mobilization?" That's a more specific and more actionable question, and in most cases, the honest answer will be no. In some cases, it won't be.
Building a Defense: Practical and Sustained
The defense against doxxing is not a single action. It is an ongoing practice of managing information exposure across multiple surfaces simultaneously. Officers who treat it as a one-time fix consistently find that their protection degrades within months as data broker listings refresh, social media posts accumulate, and new public records are generated.
The most effective approach treats personal information security the way effective threat assessment treats behavioral monitoring: as a continuous process rather than a point-in-time evaluation.
The data broker audit is the highest-leverage starting point for most officers. A systematic search of your name across major data broker sites — run by someone who doesn't know your address, to simulate what a stranger would find — will typically reveal how exposed you currently are. The removal process is time-consuming but the investment is concrete and measurable. Commercial services that manage ongoing removal across dozens of sites exist and are worth evaluating seriously for officers with meaningful threat exposure.
Social media hygiene requires a comprehensive audit of current settings across every platform, including platforms that haven't been actively used in years but still contain historical information. Privacy settings should be set to the most restrictive available option on every personal account. Location tagging should be disabled by default. Posts should be reviewed with the question: does this reveal, directly or inferentially, where I live, where my children go to school, or what my daily routine looks like? The discipline required here is genuinely inconvenient, which is why most people don't maintain it.
Metadata stripping from photographs is a technical step that requires deliberate configuration. Disabling location services for the camera application on mobile devices prevents GPS coordinates from being embedded in new photographs. For photographs already shared that may contain location data, the damage is done, but future exposure can be prevented.
Separation of professional and personal digital identity is harder to establish after the fact than before. Officers who have used the same email address, phone number, or username across both professional and personal contexts have created linkages that make aggregation easier. Where this hasn't been done, it's worth establishing going forward.
Credit freezes at all three major credit bureaus are a specific and underused protection against the identity theft dimension of doxxing. A freeze prevents new credit accounts from being opened in your name without an active unfreeze request. It takes minutes to establish and adds a meaningful barrier against one of the downstream consequences of personal information exposure.
The family briefing is not optional. What the officer has done to harden their own profile is only as effective as the weakest point in the family's collective digital presence. This conversation needs to happen, needs to be specific rather than vague, and needs to be revisited as platforms change and children age.
What Departments Owe Officers
Individual officers bear the primary responsibility for managing their own personal information exposure, but departments have obligations in this space that many are not currently meeting.
The most basic is transparency about what the department itself publishes. Departmental websites that include officer photographs and full names, press releases that name officers involved in specific incidents, and FOIA responses that include officer information without available legal exemptions all contribute to the exposure that officers are trying to manage. Departments that take doxxing seriously as an officer safety issue review what they're putting out and ensure officers are informed before their information is published.
The next obligation is training. Most departments have no formal training on personal information security, doxxing mechanics, or digital threat recognition. Officers are left to figure this out on their own or not at all. Basic digital hygiene training — delivered at the academy and refreshed periodically — is a straightforward intervention with real protective value.
Response protocols matter too. Officers who have been doxxed often don't know who to report to, what documentation to preserve, what the department will do with a report, or what support is available. The confusion and isolation that follow a doxxing incident are themselves harmful and are preventable with clear, pre-established protocols.
Finally, departments should be thinking about the psychological support dimension explicitly. Officers dealing with the aftermath of a doxxing campaign — particularly one that has included family members in the released information — are dealing with a specific kind of threat-related stress that warrants EAP access, peer support awareness, and supervisory sensitivity. Treating it as a minor administrative matter and moving on is a failure of the department's duty of care to its people.
FAQs
Is doxxing illegal?
The legal landscape is genuinely inconsistent. As of now, most states do not have laws that specifically criminalize doxxing as a standalone offense. Some states have passed or are considering anti-doxxing legislation, particularly in the context of targeting public officials. Where doxxing is accompanied by explicit threats, it may constitute criminal harassment, stalking, or threatening under existing laws. Where it results in swatting — false emergency calls designed to send armed officers to a target's location — it typically constitutes a separate criminal offense. If you've been doxxed, your department's legal counsel and local prosecutors can advise on what options exist in your jurisdiction. Document everything regardless of whether you intend to pursue it.
What should I do in the first 24 hours after discovering I've been doxxed?
Report to your department immediately — a breach of your personal security may have implications for departmental security as well, and your agency needs to know. Document all evidence of where your information has been posted before requesting removal, since removal eliminates your evidentiary record. Change all passwords and enable two-factor authentication on every account. Alert your family, with enough specificity that they understand the situation without creating unnecessary alarm. Contact data broker sites directly to request expedited removal. Brief your children's school if children's information was included in the release. If there is any explicit threat language attached to the posting, preserve it and report it to law enforcement through your normal chain of command.
How do I know if the doxxing has escalated to a credible physical threat?
This is a threat assessment question, not a checklist question. The behavioral indicators that distinguish concerning from actionable are the same ones that apply to any threat scenario: is there explicit threatening language directed at a specific person with specific information? Is there evidence of research or surveillance beyond the initial information release — someone asking for additional details, someone posting about the location? Is there any known individual in your professional history who has shown prior behavioral indicators of fixation or escalating hostility? If any of these are present, this warrants formal threat assessment involvement, not just personal vigilance. Your department's threat assessment resources, union support, and if necessary law enforcement involvement through the appropriate channels are all appropriate escalations.
Should I go public if I've been doxxed?
In most cases, no — at least not initially and not without strategic thought. Public acknowledgment of a doxxing can amplify the original distribution, signal to the doxxer that their action was effective, and invite additional attention from others who might not have seen the original posting. There are circumstances where public acknowledgment serves a purpose — particularly when the doxxing involves false or defamatory information and a correction is warranted — but those decisions should be made deliberately and ideally with legal guidance rather than reactively.
What's the most important thing I can do right now if I haven't been doxxed?
Search yourself. Use your full name, your employer, and your approximate location in a standard search engine and see what comes back. Then do the same in two or three major data broker sites. Most officers who do this for the first time are surprised by what's already publicly accessible. That baseline awareness is the starting point for everything else. What's findable about you today, before any hostile actor has begun searching, is the floor you're working from. Knowing what it is gives you the ability to prioritize where your protective effort will have the most impact.